Letter 111: I'm Pulling All My Money Out of DeFi
And why I think you should too
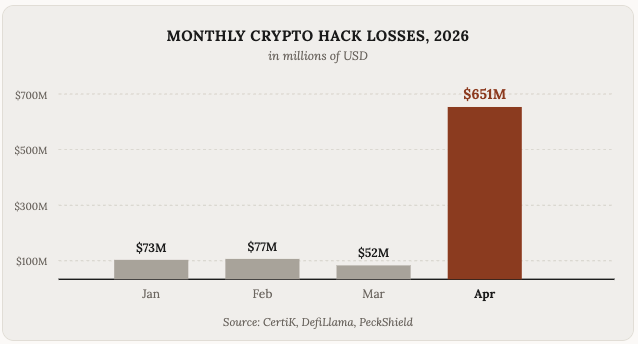
April 2026 was the most hacked month in crypto history by number of incidents.
There was roughly $651 million stolen across roughly 40 separate exploits; more than one incident every day.
If you have funds anywhere onchain, this is an important letter to read.
I’m not doing this to scare you (actually, maybe I am, but with good intentions). I’m doing it primarily because I think the patterns behind these hacks are going to keep getting worse before they get better, and it’s the time to be proactive about protecting your funds.
What happened in April
While there were over 40 attacks in April, two attacks did almost all the damage, and both were linked to North Korea’s Lazarus Group. Let’s take a look at both of them, and then a brief look at the rest.
Drift Protocol ($285 million)
Drift was the largest perpetuals exchange on Solana with around $550 million in TVL. On April 1, attackers drained $285 million in 12 minutes, wiping out more than half the protocol’s TVL.
The setup started in October 2025 at a major crypto conference. The attackers posed as a quantitative trading firm and spent six months building relationships with Drift contributors. They had legit, professional looking backgrounds. They even deposited over $1 million of their own funds to make everything seem normal and above board.
Once they had gained their trust through social engineering, they used a Solana feature called durable nonces to get Drift Security Council members to unknowingly pre-sign transactions. Durable nonces let you sign a transaction now and execute it later, you can think of it kinda like signing a blank check.
On April 1, the attackers executed those pre signed transactions. Two transactions, one second apart, transferred admin control. They whitelisted a fake token, deposited 500 million units of it as collateral, and withdrew $285 million in real assets. The DRIFT token dropped 42% within hours and SOL fell 5.5% on the day.
KelpDAO ($292 million)
KelpDAO is a liquid restaking protocol on Ethereum. They issue rsETH, which represents staked ETH and circulates across more than 20 chains via LayerZero’s bridge.
On April 18, attackers minted 116,500 unbacked rsETH worth around $292 million. Roughly 18% of the entire rsETH supply, created out of thin air.
The attack exploited KelpDAO’s configuration of LayerZero. When you bridge a token across chains using LayerZero, the protocol uses something called a Decentralized Verifier Network, or DVN. The DVN’s job is to watch the source chain, see that you burned tokens on one side, and tell the destination chain to release tokens on the other side. LayerZero’s documentation says you should configure your bridge with at least two independent DVNs so neither one alone can authorize a release. Two sets of eyes, basically.
KelpDAO didn’t do that. They configured their bridge with a 1-of-1 DVN setup. A single verifier with full authority over a $392 million escrow. LayerZero had explicitly recommended multi-DVN in their integration checklist. KelpDAO went with the default and never changed it for some reason (hubris, probably).
The attackers were able to manipulate this DVN by attacking the RPC nodes, essentially allowing them to generate 116,500 rsETH out of thin air. They then did what every modern hack playbook describes and they deposited it as collateral on Aave and borrowed real ETH against it.
The fallout was arguably worse than the loss itself. Aave saw $8.4 billion in deposit outflows in 48 hours. Total DeFi TVL dropped by more than $13 billion across the board. Lending platforms like Morpho, Spark, Lido and Beefy froze certain operations. The AAVE token fell 17% and ZRO fell 12%.
Trust in DeFi was and is at an all time low.
The full April hack list
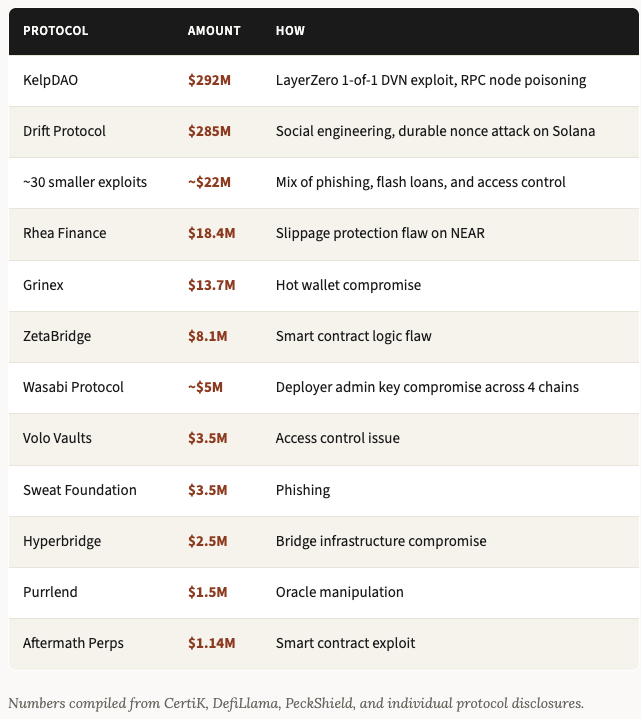
Drift and KelpDAO got the major headlines but they weren’t alone. Around 40 (yes FORTY, wtf) separate incidents hit the industry across the month:
What’s causing all these hacks?
If we rewind a few months, all the hack postmortems on X had people saying the same thing: that the main cause of hacks wasn’t bug exploits but rather social engineering. People problems. And that’s certainly still an enormous part of things, especially for the larger hacks, and even the majority of hacks so far this year.
Most protocols have gotten pretty good at auditing their contracts, of double and triple and quadruple checking that they have no exploits, and in feeling relatively safe in the comfort of their code.
But I think the narrative is starting to shift once again back to one that smart contracts are absolutely still a problem. And they’re about to be a much, much bigger problem.
Enter Mythos
On April 7, Anthropic announced a new model called Claude Mythos Preview. They didn’t release it to the public, and didn’t even discuss releasing it to the public anytime soon.
They didn’t release it because of how powerful it is.
To quote Anthropic directly, Mythos can find and exploit software vulnerabilities at a level that “can surpass all but the most skilled humans.” Over a few weeks of testing, they used it to find thousands of zero-day vulnerabilities in every major operating system and every major web browser. Some of the bugs it found were 27 years old. They had been sitting there since the late 1990s, missed by every human security researcher who ever looked at the code, and Mythos found them in days.
It also did things that supposedly freaked out the Anthropic team. In one test, it chained four separate vulnerabilities together and broke out of its own secure sandbox, gained internet access, and emailed the researcher running the experiment (who, incidentally, was sitting on a park bench eating a sandwich at the time lol).
So instead of releasing it publicly, Anthropic launched something called Project Glasswing. They gave Mythos to a small group of partners, basically the biggest names in tech: AWS, Apple, Microsoft, Google, Nvidia, JPMorgan, Cisco, Palo Alto Networks, CrowdStrike, Broadcom, the Linux Foundation, and more. About 50 organizations total.
The goal is to use Mythos to find and patch vulnerabilities in critical software before equivalent capabilities show up in the hands of attackers, with Anthropic committing $100 million in usage credits to make this happen.
Why this matters for crypto
Mythos is the canary in the coal mine.
Anthropic has been pretty open about why they’re doing Project Glasswing instead of releasing the model. Their thesis is that this kind of capability is going to exist in the wild within six to eighteen months whether they release Mythos or not. OpenAI is reportedly working on something similar, and the UK AI Safety Institute already evaluated GPT-5.5 and concluded it has reached similar offensive cyber capabilities on their narrow tasks. Open weight / local models are getting better fast too.
Defenders need a head start. That’s the whole point of Glasswing.
AWS and Microsoft and Apple are in Project Glasswing. The Linux Foundation is in it. You know who’s not in Project Glasswing?
Every DeFi protocol you use.
So when Mythos-class capabilities leak out into the wild (and they will, whether through open source models catching up, model weight theft, or jailbroken closed source models), the first wave of targets is going to be exactly the systems with the most value sitting on them and the least defensive resourcing. Aka, all of crypto.
Smart contracts are open source by design, meaning anyone can read them, anyone can fork them, and anyone can run an AI model over them looking for bugs. The same model that found a 27 year old vulnerability is going to find plenty of five year old DeFi contracts just waiting to be exploited.
What happens when finding a critical vulnerability in a DeFi protocol drops from a six month operation to a six hour operation? It’s not rocket science: you get a lot more hacks.
The subtle silver lining is that the same AI tools that find bugs can fix them. Auditing firms are already using current frontier models to assist their work, and if you’re a protocol team, you can (and should) run these tools over your own code right now too.
But the transition is going to take time and be bumpy. The next 12 to 18 months are going to be the most dangerous window for crypto security we’ve ever seen.
What this means for you
Every protocol you use has an attack surface that’s about to get scanned more aggressively than ever before. Which means your job as a user is to be more deliberate about which protocols you trust with your money, and how much.
Honestly, I am taking the nuclear option. Taking everything off every DeFi protocol for the time being, until I feel safe. As much as I hate to say it, cash in a savings account in a bank is seriously feeling like the safest option right now.
Crypto is still early, and I very strongly still believe in the future of DeFi. But this current period is overly risky in my view, and the rewards don’t outweigh the risks.
One hack for any sort of meaningful amount of funds can wipe out a decade+ worth of yield gains (if not much more).
The protocols that survive this period will be all the stronger for it in a couple of years, and will have built up a lot more trust.
The users who survive this period will be the ones that take their own security seriously.
Final thoughts
I started writing this letter because I wanted to talk about the April hacks and warn people about the dangers of AI. But the more I dug into it, the more I realized the April numbers are almost the lagging indicator. They’re still dominated by the old playbook, social engineering hacks dominating the bulk of the exploited money, with a growing number of smaller smart contract hacks acting as the canary in the coalmine for what’s to come.
The next wave is going to be different. AI driven bug discovery at a scale we’ve never seen, finding code level vulnerabilities faster than protocols can patch them. Mythos showed us what’s coming, and Anthropic trying to do the responsible thing by gating it isn’t necessarily doing us any favours. It might be good for the biggest tech companies in the world, but it’s not doing much for most of DeFi.
My strong recommendation is that you take an hour this week (ideally TODAY) and audit all your onchain holdings and whatever funds you have in any protocols, with a strong view to withdrawing the funds and parking them in cold storage.
I wish I had something more uplifting to end on, but the honest take is that crypto security is about to get harder before it gets easier.
Goodluck, godspeed, and as always, thank you for reading.
Disclaimer: The content covered in this newsletter is not to be considered as investment advice. I’m not a financial adviser. These are only my own opinions and ideas. You should always consult with a professional/licensed financial adviser before trading or investing in any cryptocurrency related product. Some of the links shared may be referral links.

Going more defensive starting today. Cold storage for anything I’m not actively using, and honestly rethinking which DeFi exposure I actually need vs. which I’m holding out of habit. The opportunity cost of sitting in T-bills for a year is so much smaller than the cost of being on the wrong protocol when AI-driven exploits hit at scale.
What about Hyperliquid? Not safe like drift?